Just for the record. They are old, they are good, but they are end of life and we don’t use them any more.
Category Archives: Network
Cisco ASA and lot of email recipients
Those days we faced the problem that we recived a mail with approx 150 recipients.
Somewhere in the communication it seams that a mail address is broken by the asa.
On the Outside of the ASA you see following in the trace:
Inside E-Mail Server (Blue) mail.example.com
Outside E-Mail Server (Red) mail.asdf.com
220-mail.example.com ESMTP Server [Wed, 18 Aug 2010 10:30:58 +0200]
220-Ready to recycle your bits, but we don't want
220 your unsolicited or bulk e-mail (ie: spam)
EHLO mail.asdf.com
250-mail.example.com Hello mail.asdf.com [192.168.0.1]
250-SIZE 4194304
250-PIPELINING
250-AUTH PLAIN LOGIN CRAM-MD5 NTLM
250-STARTTLS
250 HELP
MAIL FROM:<asdf@asdf.com> SIZE=42157
RCPT TO:<user1@example.com>
<output omited>
RCPT TO:<user20@example.com>
RCPT TO:<user21@
250 OK
example.com>
RCPT TO:<user22@example.com>
RCPT TO:<user23@example.com>
RCPT TO:<user24@example.com>
<output omited>
250 Accepted
<output omited>
250 Accepted
501 <user21@XXXXXXXXXXXXXX: '>' missing at end of address
250 Accepted
250 Accepted
250 Accepted
On the Inside of the ASA you see following in the trace:
Inside E-Mail Server (Blue) mail.example.com
Outside E-Mail Server (Red) mail.asdf.com
220-mail.example.com ESMTP Server [Wed, 18 Aug 2010 10:30:58 +0200]
220-Ready to recycle your bits, but we don't want
220 your unsolicited or bulk e-mail (ie: spam)
EHLO mail.asdf.com
250-mail.example.com Hello mail.asdf.com [192.168.0.1]
250-SIZE 4194304
250-PIPELINING
250-AUTH PLAIN LOGIN CRAM-MD5 NTLM
250-STARTTLS
250 HELP
MAIL FROM:<asdf@asdf.com> SIZE=42157
RCPT TO:<user1@example.com>
<output omited>
RCPT TO:<user20@example.com>
RCPT TO:<user21@ 250 OK
XXXXXXXXXXXXXX
RCPT TO:<user22@example.com>
RCPT TO:<user23@example.com>
RCPT TO:<user24@example.com>
<output omited>
250 Accepted
<output omited>
250 Accepted
501 <user21@XXXXXXXXXXXXXX: '>' missing at end of address
250 Accepted
250 Accepted
250 Accepted
This is a little bit strange so i will ask the Guys from Cisco if this is a known feature or a bug.
For the Momemt we have disabled the esmtp fixup, on monday we will do future analysis.
If you feel this helps a bit or may be not ? Please leave a comment.
Wireshark (tshark)
Just capture files with 100MB each:
[sourcecode]
tshark -i eth2 -b filesize:100000 -w eth2_smtp.pcap -s 0 -R "smtp"
[/sourcecode]
If you feel this helps a bit or may be not ? Please leave a comment.
Enterasys C2 SNMPv2
[sourcecode]
set snmp access gReadOnlyV1V2C security-model v1 exact read vUnsecured
set snmp access gReadOnlyV1V2C security-model v2c exact read vUnsecured
set snmp community mycomunity securityname sn_v1v2c_ro
set snmp group gReadOnlyV1V2C user sn_v1v2c_ro security-model v1
set snmp group gReadWriteV1V2C user sn_v1v2c_rw security-model v1
set snmp group gReadOnlyV1V2C user sn_v1v2c_ro security-model v2c
set snmp group gReadWriteV1V2C user sn_v1v2c_rw security-model v2c
set snmp view viewname vUnsecured subtree 1
set snmp view viewname vUnsecured subtree 0.0
[/sourcecode]
If you feel this helps a bit or may be not ? Please leave a comment.
Enterasys C2 and SSH
To enable the SSH Service on a Enterasys SecureStack C2 and similar you have to issue “set ssh enabled” on the cli.
[sourcecode autolinks=”false” gutter=”false” highlight=”2″]
C2(su)->set ssh enabled
SSH hostkey generation initiated. Process should complete in 60 seconds.
C2(su)->
[/sourcecode]
If you feel this helps a bit or may be not ? Please leave a comment.
Cisco ASA and Tacacs+
How to use Tacacs+ on Cisco ASA for Shell and Web Authentication
Assume the Tacacs+ Servers are:
| Cisco ACS Server 1 | 10.120.10.11 |
| Cisco ACS Server 2 | 10.120.10.12 |
[sourcecode gutter=”false” autolinks=”false”]
aaa-server AAA-TACACS+ protocol tacacs+
!
aaa-server AAA-TACACS+ (Management) host 10.120.10.11
key YYYYXXXYYY
!
aaa-server AAA-TACACS+ (Management) host 10.120.10.12
key YYYYXXXYYY
!
! Delete the old local only configuration
no aaa authentication http console LOCAL
no aaa authentication ssh console LOCAL
!
aaa authentication http console AAA-TACACS+ LOCAL
aaa authentication ssh console AAA-TACACS+ LOCAL
aaa authentication enable console AAA-TACACS+ LOCAL
aaa authorization command AAA-TACACS+ LOCAL
!
[/sourcecode]
If you have allready configured aaa for the ssh you might see something like
[sourcecode autolinks=”false” gutter=”false” highlight=”2″]
asa1(config)# aaa authentication ssh console AAA-TACACS+ LOCAL
Range already exists.
[/sourcecode]
Then you must first disable the aaa authentication and than add the new settings.
[sourcecode autolinks=”false” gutter=”false”]
no aaa authentication ssh console LOCAL
aaa authentication ssh console AAA-TACACS+ LOCAL
[/sourcecode]
If you feel this helps a bit or may be not ? Please leave a comment.
Cisco ASA and SMTP
We recently bought so new Firewalls to replace to aged Cisco PIX515e with some new Gear. We decided to use Ciscos new Firewall flagship the Cisco ASA Devices. Everything was fine after the replacement, we transfered the configuration from the old boxes to the new with the help of the Cisco Security Manager.
Later that day there was complains about e-mails are not delivered properly.
On the Cisco PIX with Software 6.2 we had implemented following:
no fixup smtp
For the ASA5510 we had to implement following
policy-map type inspect esmtp esmtp_pmap
parameters
allow-tls action log
policy-map global_policy
class inspection_default
no inspect esmtp
inspect esmtp esmtp_pmap
exit
exit
If you feel this helps a bit or may be not ? Please leave a comment.
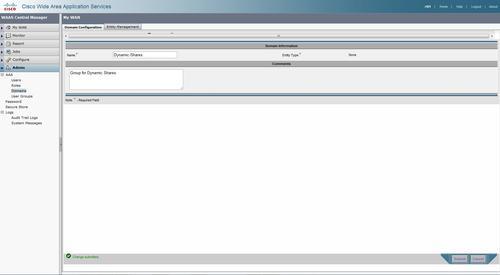
Access-based Enumeration (ABE) and Cisco WAAS
Access-based Enumeration (ABE) is a smart feature to let users see only the folders they have access to.
But if you have Cisco WAAS deployed in your network please be aware you have to add a Dynamic share to the waas configuration so the waas knows about this.
—– EDIT BEGIN —–
2010-09-17 We found out the Hardway you have to add the System to the AD. So i will show the Story in a new Post:-) Stay tuned, guys.
—– EDIT END ——-
Cisco Wide Area Application Services Configuration Guide (Software Version 4.1.7)
Step 1
For creating a dynamic share you have to add a Domain to the Cental Manager eg “Dynamic Shares”
Step 2
Create a entry under the dynamic shares in the global configuration.
On the WAE CLI
ToBe Done
If you feel this helps a bit or may be not ? Please leave a comment.
Cisco MDS 9222i with ACS
If you want to configure tacacs+ on the Cisoc MDS9222i Series you have to enable first the feature.
[sourcecode autolinks=”false” gutter=”false”]
feature tacacs+
[/sourcecode]
After this the commands to configure the Tacacs+ are available.
[sourcecode autolinks=”false” gutter=”false”]
feature tacacs+
!
tacacs+ distribute
tacacs-server timeout 10
tacacs-server host 10.0.243.247 key 0 secertkey
tacacs-server host 10.0.243.248 key 0 secretkey
tacacs+ commit
!
aaa group server tacacs+ AAA-Servers
server 10.0.243.247
server 10.0.243.248
deadtime 5
!
aaa authentication login default group AAA-Servers
aaa authentication login console local
aaa authentication login error-enable
!
ip route 10.0.243.247 255.255.255.255 10.0.160.1 interface mgmt0
ip route 10.0.243.248 255.255.255.255 10.0.160.1 interface mgmt0
!
interface mgmt0
ip address 10.0.160.99 255.255.255.0
switchport description Management
switchport speed 100
[/sourcecode]
On the ACS side you have to configure the shell profile with the following role:
[sourcecode autolinks=”false” gutter=”false”]
shell:roles="network-admin"
[/sourcecode]
If you feel this helps a bit or may be not ? Please leave a comment.
Cisco WAAS and Tacacs+
Configuration with the Central Manager
tacacs key **** tacacs host 10.0.243.247 primary tacacs host 10.0.243.248 tacacs key **** authentication login local enable secondary authentication login tacacs enable primary authentication configuration local enable secondary authentication configuration tacacs enable primary authentication fail-over server-unreachable aaa authorization commands 15 default tacacs+